UK Unmasks High-Ranking Russian Hacker as Part of the LockBit Ransomware Group
- A high-ranking affiliate of the LockBit ransomware gang was revealed to be an alleged leader of Evil Corp.
- The individual’s right hand was indicted by the U.S. for conducting ransomware attacks.
- Meanwhile, two other hackers linked to LockBit have been caught in Europe.
The U.K. unmasked a high-ranking affiliate of the notorious LockBit ransomware group, tied to Russia's state-backed cyber activities, according to the latest report from Reuters. This is part of a broader action against Evil Corp, a Russian cybercrime gang long believed to be a formidable threat on the global stage.
Maksim Yakubets, alleged leader of Evil Corp, is known for his ties with Russia’s Federal Security Service (FSB), Foreign Intelligence Service (SVR), and military intelligence unit GRU. His father-in-law, Eduard Benderskiy, an ex-FSB official, is accused of enabling the group's activities.
The U.S. Department of Justice (DoJ) indicted Aleksandr Ryzhenkov, known as “Beverley,” identified as a LockBit affiliate and Yakubets' right-hand man, for ransomware attacks using the BitPaymer strain in Texas and other locations.
The U.K., the U.S., and Australia also sanctioned 16 members of Evil Corp, targeting individuals involved in cyber-attacks and espionage against NATO allies.
The Director General for Threats at the UK's National Crime Agency (NCA) highlighted the link between Evil Corp and LockBit, which has notoriously targeted organizations such as Boeing and Britain's Royal Mail.
At the same time, European authorities announced the arrest of two additional individuals with ties to the LockBit ransomware empire - one in France and one in Spain.
LockBit has functioned as a Ransomware-as-a-Service (RaaS) affiliate-based variant since January 2020 and was set up by a Russian coder from Voronezh named Dimitri Khoroshev, who uses online aliases like Putinkrab, Nerowolfe, and LockBitSupp, whose assets were frozen by law enforcement in early May.
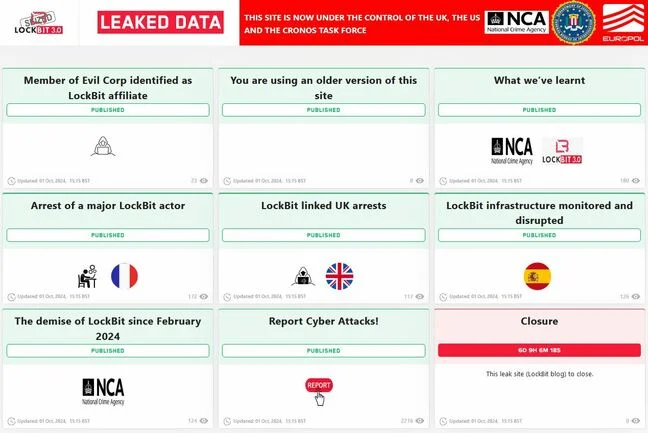
In February 2024, law enforcement shut down the infrastructure of the LockBit RaaS affiliate-based variant through Operation Cronos. Authorities seized several servers that contained decryption keys and offered approximately 7,000 LockBit keys to U.S. and international victims.
Throughout these years, LockBit affiliates have attacked numerous businesses and critical infrastructure organizations in the United States and internationally, deploying LockBit via various tools, techniques, and procedures.
The threat group targeted several enterprises throughout the years, including multinationals such as consulting firm Accenture, from which the actors claimed to have stolen 6 terabytes of data worth $50 million in ransom payment.
Since the debut version, LockBit 1.0, the ransomware strain has released newer versions such as LockBit 2.0 (LockBit Red), LockBit 3.0 (LockBit Black), LockBit Linux/ESXI, and LockBit Green, while LockBit 4.0 is reportedly under development.