‘Salvador Stealer’ Targets Banking Customers with Sophisticated Malware
- Novel Salvador Stealer targets banking customers with SMS interception and OTP theft.
- It uses a phishing interface and relies on real-time data exfiltration of user IDs and passwords.
- This resilient Android-based malware is a multi-stage attack tool that masquerades as a legitimate mobile banking app.
A new Android-based malware strain designed to harvest sensitive personal and financial information, dubbed Salvador Stealer, showcases advanced capabilities for targeting mobile banking app users.
This malware is a multi-stage attack tool that embeds a phishing website and hijacks SMS messages. Salvador Stealer collects sensitive user information, including:
- Registered mobile number
- Aadhaar number
- PAN card details
- Date of birth
- Net banking user ID and password
These details have led to speculative links to India, though attribution remains unclear.
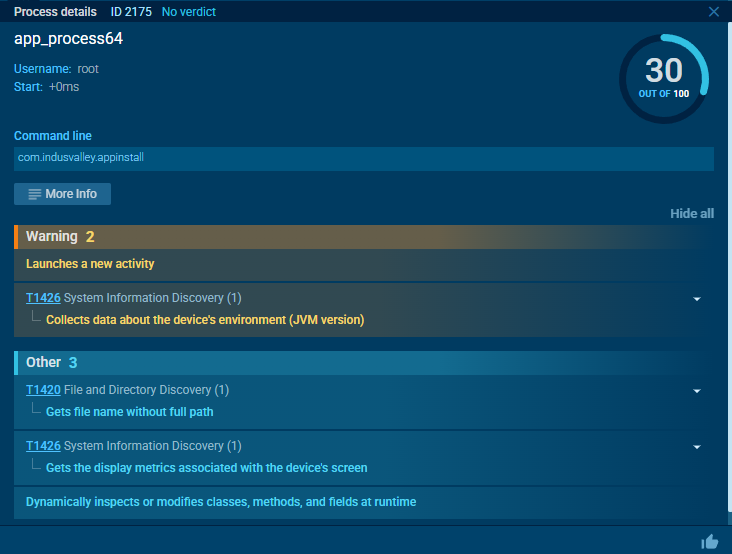
Uncovered and analyzed by the team at ANY.RUN, Salvador Stealer employs a two-stage infection process using a dropper APK, which silently installs and activates the malicious payload, base.apk, on the victim's device.
The malware masquerades as a legitimate mobile banking app, tricking users into entering their credentials into a fake interface. Once entered, this data—including banking credentials, Aadhaar numbers, and even OTPs (one-time passwords)—is instantly exfiltrated to the attackers via multiple channels.
Salvador Stealer integrates a well-designed phishing interface directly within the application to deceive users into providing their banking credentials.
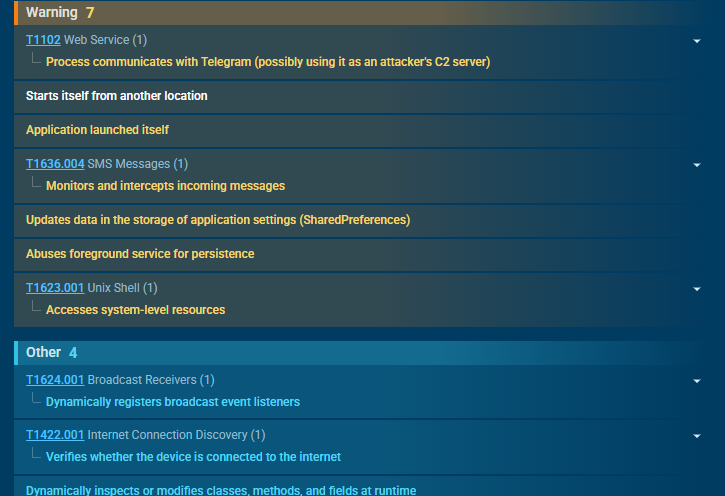
Armed with permissions to intercept incoming SMS messages, the malware captures OTPs sent via text for verification, allowing attackers to bypass two-factor authentication.
Victim credentials are sent to both a phishing server and a C2 (Command and Control) server controlled via the Telegram Bot API.
The malware employs advanced persistence mechanisms, such as restarting itself if terminated and surviving device reboots via system-level broadcast receivers.
The analysis also revealed interesting insights into Salvador Stealer’s infrastructure. The phishing websites and administrative control panels used by the attackers were found to expose sensitive information, including a WhatsApp number linked to a possible operator of the malware.