Fake Google Meet Errors Distribute Infostealing Malware Like StealC and Rhadamanthys
- Hackers employ fake Google Meet conference errors to distribute malware backed by social engineering.
- Windows and macOS users in the U.S. and Japan are targeted with infostealers delivered as fake fixes for online conference errors.
- The campaign, ClickFix, seems to be extending to impersonating Zoom, PDF readers, video games, web3 browsers, and messenger applications.
A recent surge in cyber threats has been identified involving fake Google Meet conference errors, which are being used to deliver infostealing malware across Windows and macOS platforms. This campaign, known as ClickFix, is a sophisticated social engineering tactic that first emerged in May and was initially flagged by cybersecurity firm Proofpoint.
According to a report from Sekoia, these campaigns have become more prevalent, particularly in the United States and Japan, and now extend beyond Google Meet. The attackers have also been using fraudulent platforms mimicking Zoom, PDF readers, fake video games, web3 browsers, and messenger applications to distribute malware.
The ClickFix campaign has evolved significantly, posing a heightened risk to users worldwide, particularly within corporate environments that rely heavily on video communication services like Google Meet.
The threat actors behind these attacks, namely TA571 and new groups identified as the Slavic Nation Empire (SNE) and Scamquerteo, target victims through phishing emails that mimic legitimate Google Meet invitations. These gangs are believed to be sub-teams of the cryptocurrency scam gangs Marko Polo and CryptoLove.
These emails are primarily directed at sectors such as transport and logistics, leveraging the familiarity and trust associated with Google Meet links to dupe users into downloading malicious software.
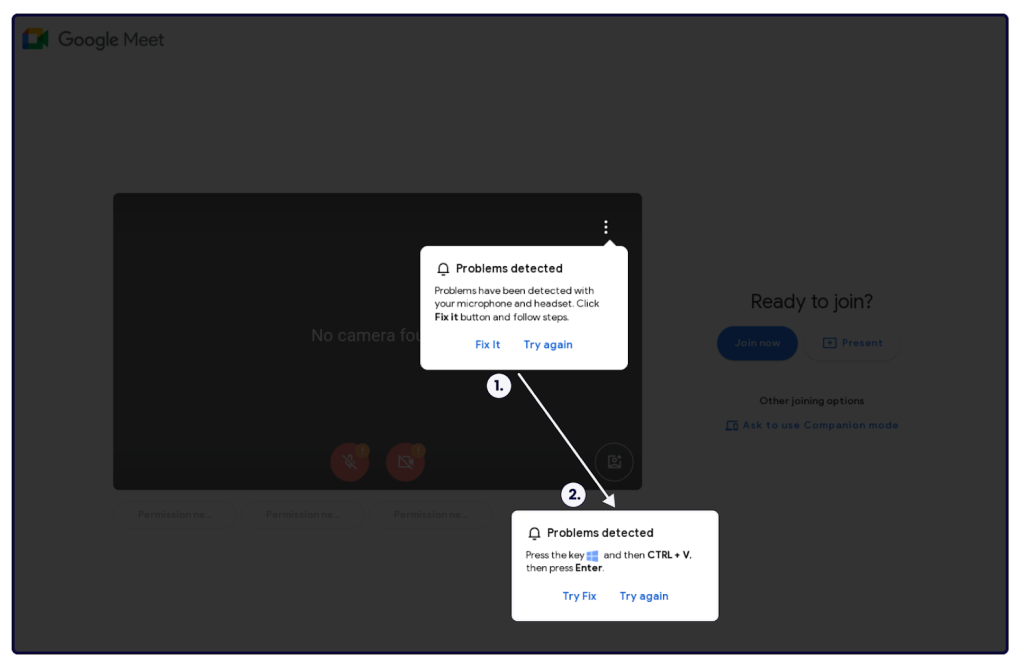
Upon clicking the fraudulent Google Meet link, victims encounter a pop-up error message suggesting a technical issue, such as a microphone malfunction. The "Try Fix" button initiates the typical ClickFix infection process, prompting users to execute PowerShell code that covertly installs malware on their systems.
This attack vector primarily delivers StealC or Rhadamanthys malware on Windows devices, while macOS users face the AMOS Stealer embedded in a .DMG file.
In other news, a unique social engineering campaign uses fake Google Chrome errors to ask potential victims to copy malicious PowerShell scripts that deploy malware on their computers, including DarkGate, Matanbuchus, NetSupport, and various infostealers.