DragonForce Ransomware Claims Expansion Amid Alleged RansomHub Takeover
- DragonForce announced the takeover of the infamous RansomHub ransomware, which is to be incorporated into its infrastructure.
- The threat actor made the announcement on a well-known dark web forum and its leak website.
- Meanwhile, RansomHub’s official onion site has been offline since last month.
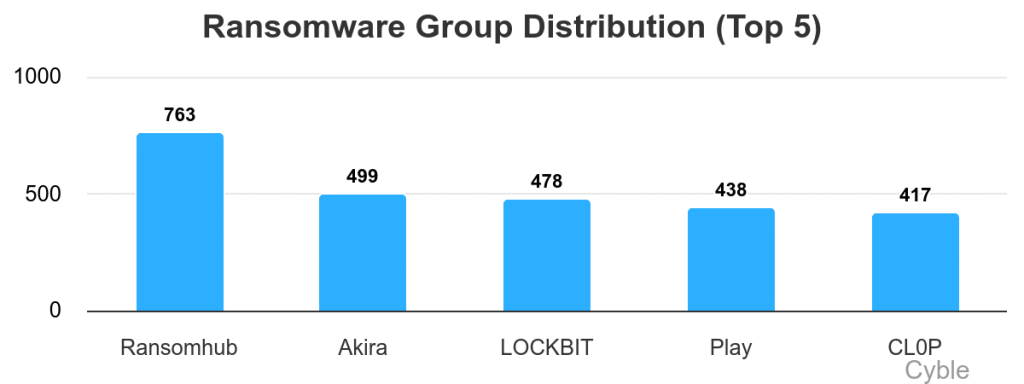
The DragonForce ransomware group has publicly announced plans to take control of RansomHub’s infrastructure, the largest ransomware group dominating attacks over the last year.
This claim was reported by Cyble’s threat intelligence team in an advisory that says DragonForce made its announcement through RAMP, a well-known forum in darknet circles, as well as via the group’s Tor-based Data Leak Site (DLS).
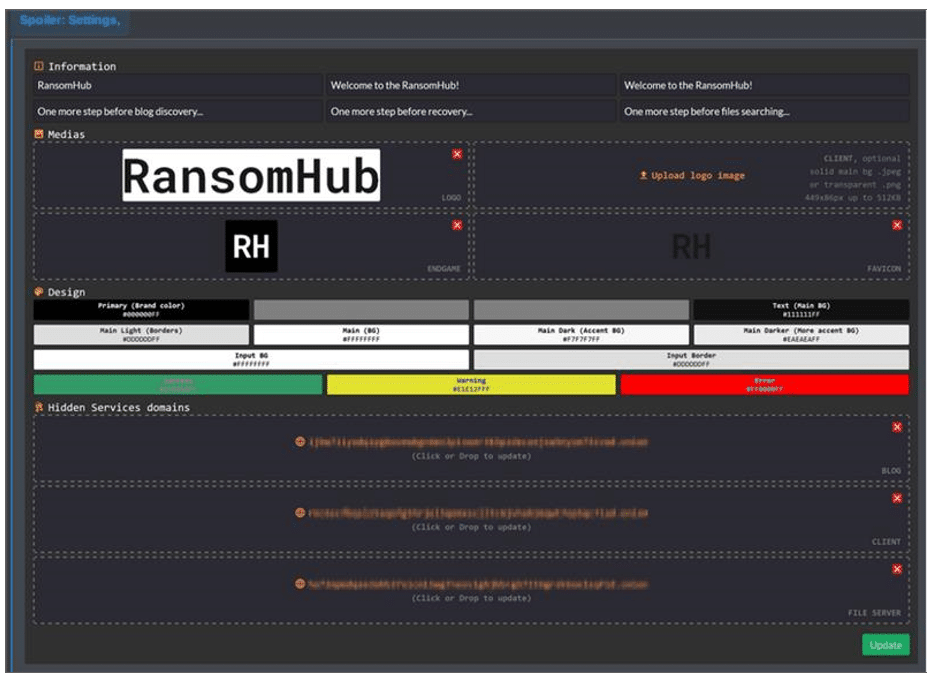
The group outlined its “new project,” revealing its intention to incorporate RansomHub into its infrastructure. DragonForce also previewed updated Onion links secured by CAPTCHA prominently featuring RansomHub’s logo, suggesting the integration is already underway.
While the nature of the relationship between DragonForce and RansomHub remains unclear, the timing is noteworthy. RansomHub’s official onion site has been offline since March 31, raising suspicions about a possible compromise or acquisition.
Cyble noted that DragonForce has not clarified whether this is a merger, hostile takeover, or infiltration.
This announcement follows DragonForce’s recent move to expand its ransomware-as-a-service (RaaS) operation, announced just weeks earlier on March 18. DragonForce introduced an affiliate model allowing “franchisees” to launch malicious campaigns under the DragonForce banner.
Affiliates are said to benefit from full backend support, anti-DDoS protection, enhanced encryption mechanisms, and tools for managing ransomware infections across systems, including ESXi, NAS, BSD, and Windows.
These developments point to DragonForce’s ambition to professionalize and scale its operations within the cybercrime landscape. Enhancements such as encryption monitoring and persistent messaging for victims signal a move toward a more business-like and robust ransomware infrastructure.
Whether RansomHub will continue under the DragonForce umbrella or reemerge independently remains to be seen. For now, the situation suggests a possible consolidation within the ransomware market, potentially leading to increased operational sophistication among threat actors.