Black Basta & Cactus Ransomware Leverage MS Teams, Quick Assist, BackConnect in New Campaign
- The Black Basta and Cactus ransomware groups added the use of BackConnect malware.
- This addition significantly bolsters their control over compromised systems and enables data exfiltration at a new level of sophistication.
- Attackers rely on social engineering tactics, cloud exploitation, and abuse of legitimate tools in their new campaigns.
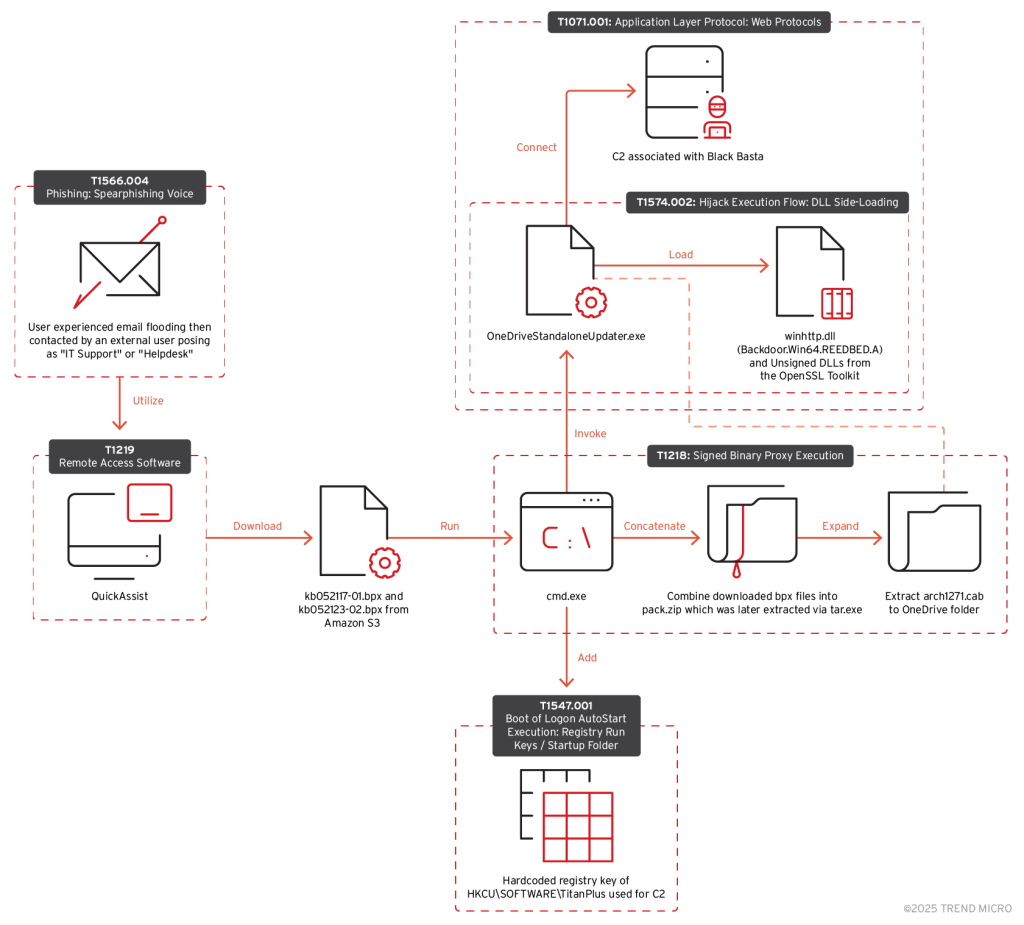
The Black Basta and Cactus ransomware groups have integrated BackConnect malware into their arsenal. Attackers leveraged social engineering via tools like Microsoft Teams, impersonating IT support to convince victims to grant access using remote tools such as Quick Assist.
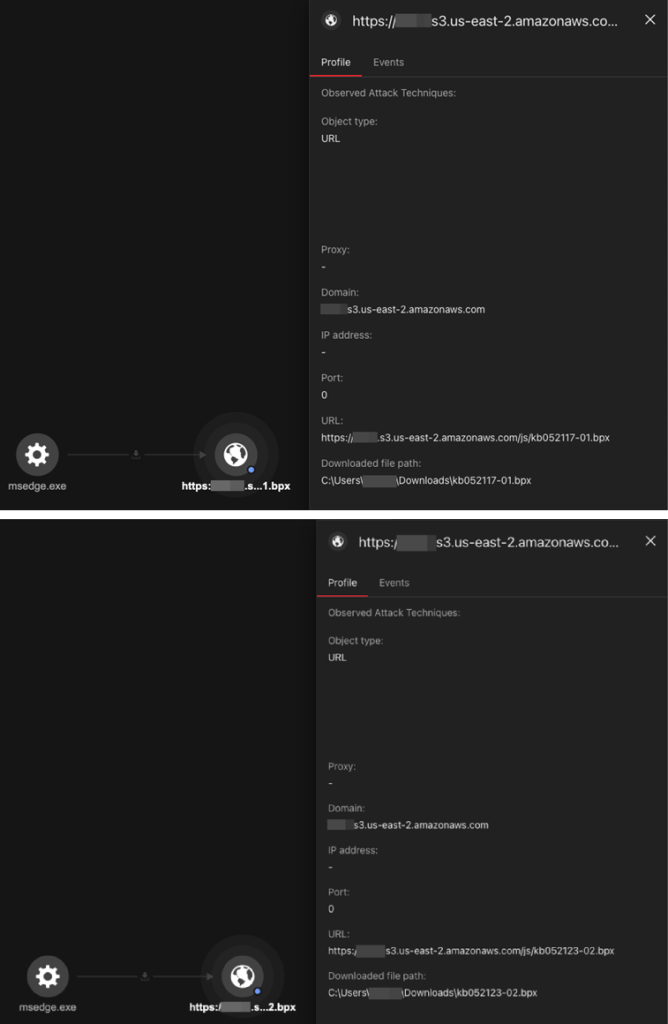
The OneDriveStandaloneUpdater.exe file was exploited to side-load malicious DLLs, granting unauthorized access to internal networks. The report says commercial cloud storage services were utilized to host and distribute malicious files, taking advantage of misconfigured or publicly accessible storage buckets.
The new strain of BackConnect malware (detected as QBACKCONNECT by Trend Micro) exhibits links to the previously dismantled QakBot, a notorious loader malware, suggesting a pivot in attack methodologies following QakBot's takedown in 2023.
The attackers' methodology emphasizes layering traditional attack vectors with modern tactics. BackConnect malware enables cybercriminals to maintain persistent remote control over infected devices.
Its capabilities include executing commands, exfiltrating sensitive data (e.g., login credentials and financial information), and ensuring unauthorized access long after initial infiltration.
This makes it a powerful tool for threat actors seeking to blend malicious activities into normal business operations undetected.
According to Trend Micro Threat Intelligence, 39 incidents involving these groups were recorded since October 2024, with North America accounting for 21 breaches. Manufacturing was the most targeted sector, with 10 recorded attacks, followed by financial consulting and real estate (six victims each).
In January, a Sophos security report revealed that two ransomware threat actors, STAC5143 and STAC5777, leveraged MS 365 services and exploited default MS Teams configurations to breach organizations' systems. Once inside, they downloaded a ProtonVPN executable or legitimate MS executables and sideloaded a malicious DLL.