Key TakeawaysData Compromised: The Kemper Corporation data breach exposed nearly 270,000 unique email addresses and associated details.Extortion Campaign: ShinyHunters targeted Kemper Corporation in an April…

Key TakeawaysAdvanced Spoofing Campaigns: The FBI warns that threat actors are spoofing FIFA domains ahead of the global tournament.Typo Squatting Tactics: Malicious actors utilize typo…

Key TakeawaysVulnerability Exploited: Arctic Wolf Labs detected CVE-2026-35616 exploitation against FortiClient EMS deployments in May 2026.Payload Disguised as a Fix: Threat actors delivered the EKZ…

Key TakeawaysDarknet Distribution Ring: Four Massachusetts men were sentenced to over 57 years for manufacturing and distributing counterfeit pills via darknet marketplaces.Lethal Synthetic Opioids: The…

Key TakeawaysAccount Compromise Detected: Carnival Corp identified a breach stemming from an employee account in April.Sensitive Data Exposed: The cruise operator intrusion reportedly occurred via…
Key TakeawaysDeceptive Tactics: Cybercriminals abuse Adobe infrastructure to harvest LinkedIn credentials.Malicious Attachments: Fake contract files use double extensions and obfuscated JavaScript.Victim Tracking: A domain associated…

Key TakeawaysSuspect Apprehended: The Dutch National Police arrested a 35-year-old man for multiple AFC Ajax IT intrusions.Vulnerability Exploited: An attacker exploited vulnerabilities to access APIs…

Key TakeawaysMassive Data Breach: Attackers compromised over 600,000 records from the Centre of Registers.Credential Misuse Detected: The intrusion leveraged unauthorized access via institutional login credentials.Leadership…

Key TakeawaysMassive Data Exfiltration: ShinyHunters said it stole over 200GB of compressed data from Ameriprise Financial in MarcExtortion Campaign Execution: After ShinyHunters leaked data post-negotiations,…

Key TakeawaysCritical Data Compromise: UK Visa Portal reportedly exposed at least 100,000 sensitive applicant records.Independent Third-Party Entity: The platform operates externally from the official GOV.UK…

Key TakeawaysVulnerability Exploited: Mandiant announced that attackers exploited the CVE-2026-5426 in the KnowledgeDeliver platform.ViewState Vulnerability Exploited: Attackers leveraged CVE-2026-5426 via hardcoded ASP.NET machine keys to…
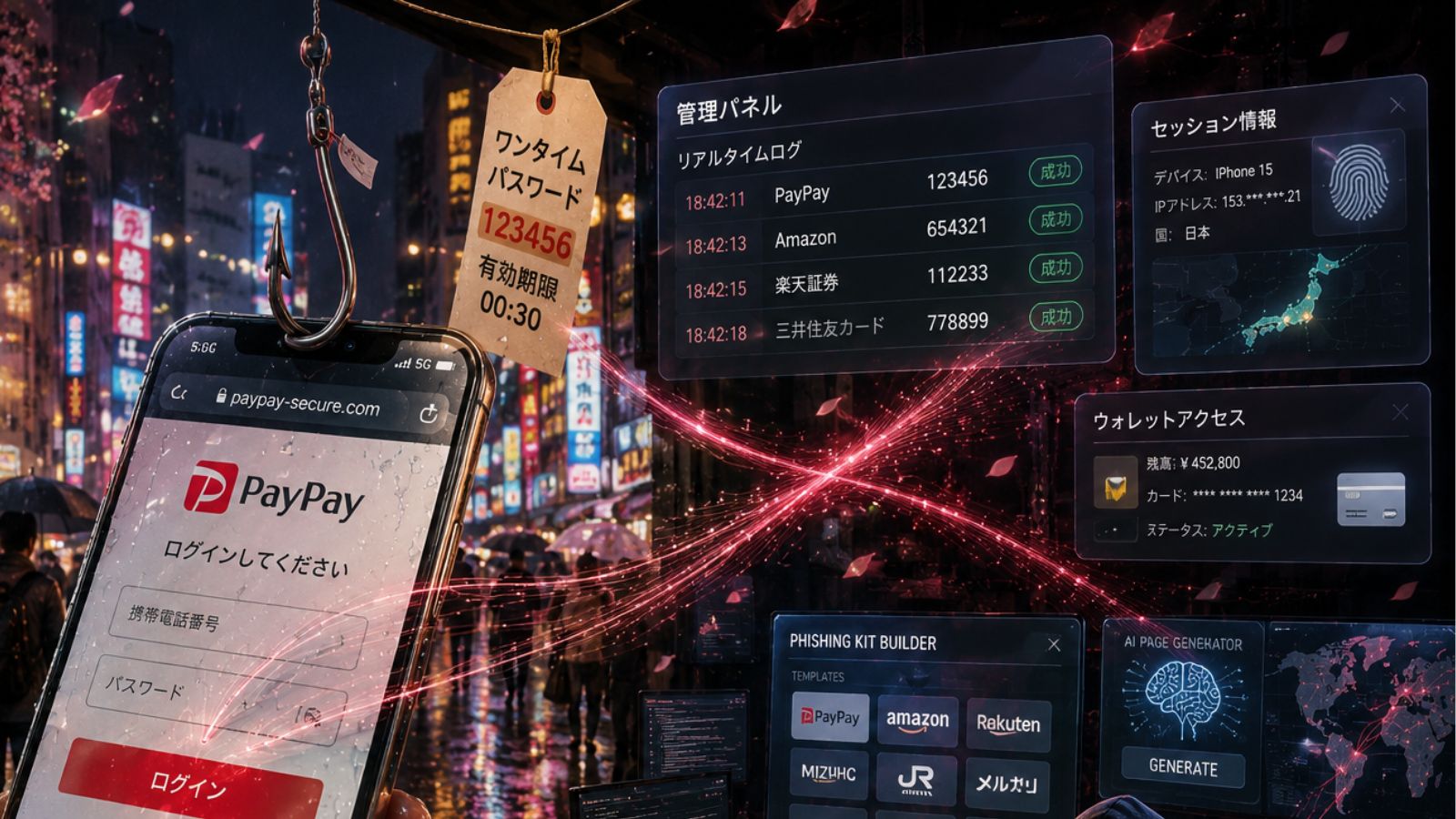
Key TakeawaysEcosystem Expansion: Google Threat Intelligence Group analysis reveals rapid growth in Chinese-language phishing-as-a-service platforms.Authentication Bypass: Attackers leverage live administration panels to capture one-time passcodes…

Key TakeawaysHosting Infrastructure Seized: Dutch authorities confiscated over 800 servers linked to Russian cyber operations.Suspects Arrested: FIOD detained two individuals for allegedly violating EU sanctions…

Taiwan Cyber Incidents in 2025: Fake Messaging Apps, Custom Ransomware, Supply Chain Vulnerabilities
Key TakeawaysIncident Volume: Taiwan documented over 700 governmental cybersecurity incidents throughout the 2025 fiscal period.Threat Vectors: Unauthorized access remains the primary driver, accounting for almost…

Key TakeawaysMulti-Registry Campaign: A supply chain attack tracked as TrapDoor targets developers via npm, PyPI, and Crates.io packages.Extensive Credential Theft: The malware steals SSH keys,…

Key TakeawaysExtortion Campaign: The ShinyHunters pay-or-leak attack against 7-Eleven resulted in the compromise of over 185,000 unique email addresses and personal details.System Scope: 7-Eleven stated…

Key TakeawaysCritical Vulnerability Exploitation: Threat actors are actively leveraging CVE-2026-26980 within Ghost CMS to execute ClickFix attack workflows.Extensive Domain Compromise: XLab threat intelligence has identified…

Steffan Tomlinson - Cyera Steffan Tomlinson became a board member at Cyera, an AI security company focused on data protection and exposure management. He currently…

Key TakeawaysX-VPN Membership Update: X-VPN joined VPN Trust Initiative and i2Coalition to support industry privacy and security standards.Industry Collaboration: Memberships help X-VPN align with transparency,…