Key TakeawaysData Breach Scale: World Food Programme said a data breach exposed sensitive information belonging to about 600,000 Palestinian households in Gaza.Platform Suspended: WFP temporarily…
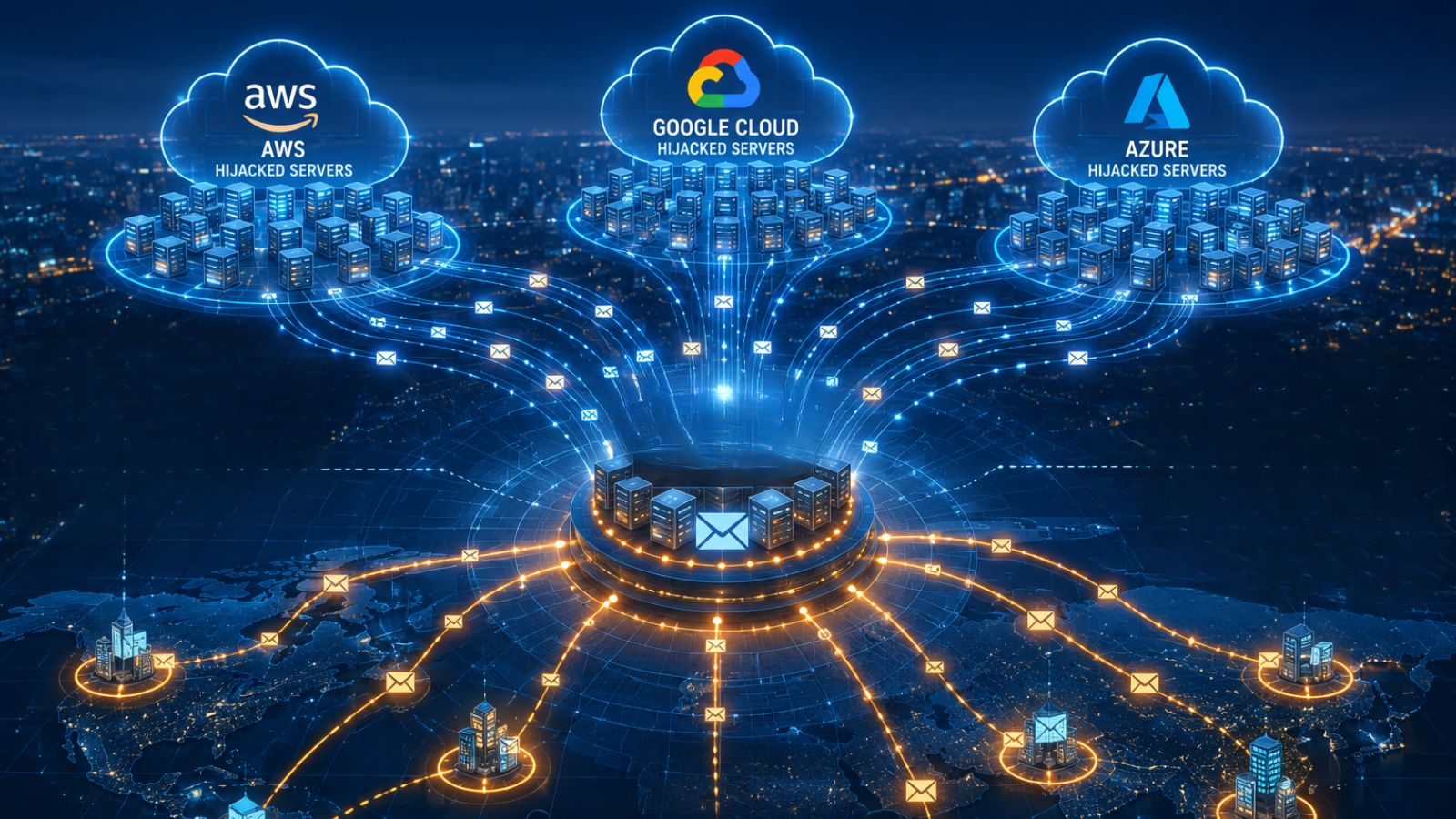
Key TakeawaysCloud Infrastructure Hijacked: PCPJack reportedly compromised 230 servers across AWS, Google Cloud, and Azure to build a covert SMTP relay network.Proxy Sync Interval: The…

Key TakeawaysAI-Discovered Exploit: OpenAI's Codex agent helped uncover the HTTP/2 Bomb, a remote denial-of-service exploit targeting default HTTP/2 server configurations.Massive Attack Surface: More than 880,000…

Key TakeawaysFive-Month Campaign: Attackers targeted a major global stock exchange senior executive's Outlook mailbox over a five-month period.Cloud-Based Exfiltration: Data was stolen in incremental batches…
Key TakeawaysJapan social media age restrictions: Government proposes stronger age verification without imposing a blanket under-16 social media ban.Platform-specific approach: Different social media platforms could…

Key TakeawaysShinyHunters Extortion: DentaQuest was targeted by ShinyHunters in May 2026, resulting in hundreds of gigabytes of data being publicly published.Data Exposure: The leaked dataset…

Key TakeawaysNotification-Based Hijack: WhatsApp, Slack, Signal, Instagram, SMS, and Messenger notifications could be used to hijack Google Gemini via indirect prompt injections.No App Required: Poisoned…

Key TakeawaysMalware-Driven Breach: Hackers accessed Ultrahuman customer wellness data using credentials stolen from a malware-infected employee laptop.Limited Scope Confirmed: Ultrahuman said no passwords, payment information,…
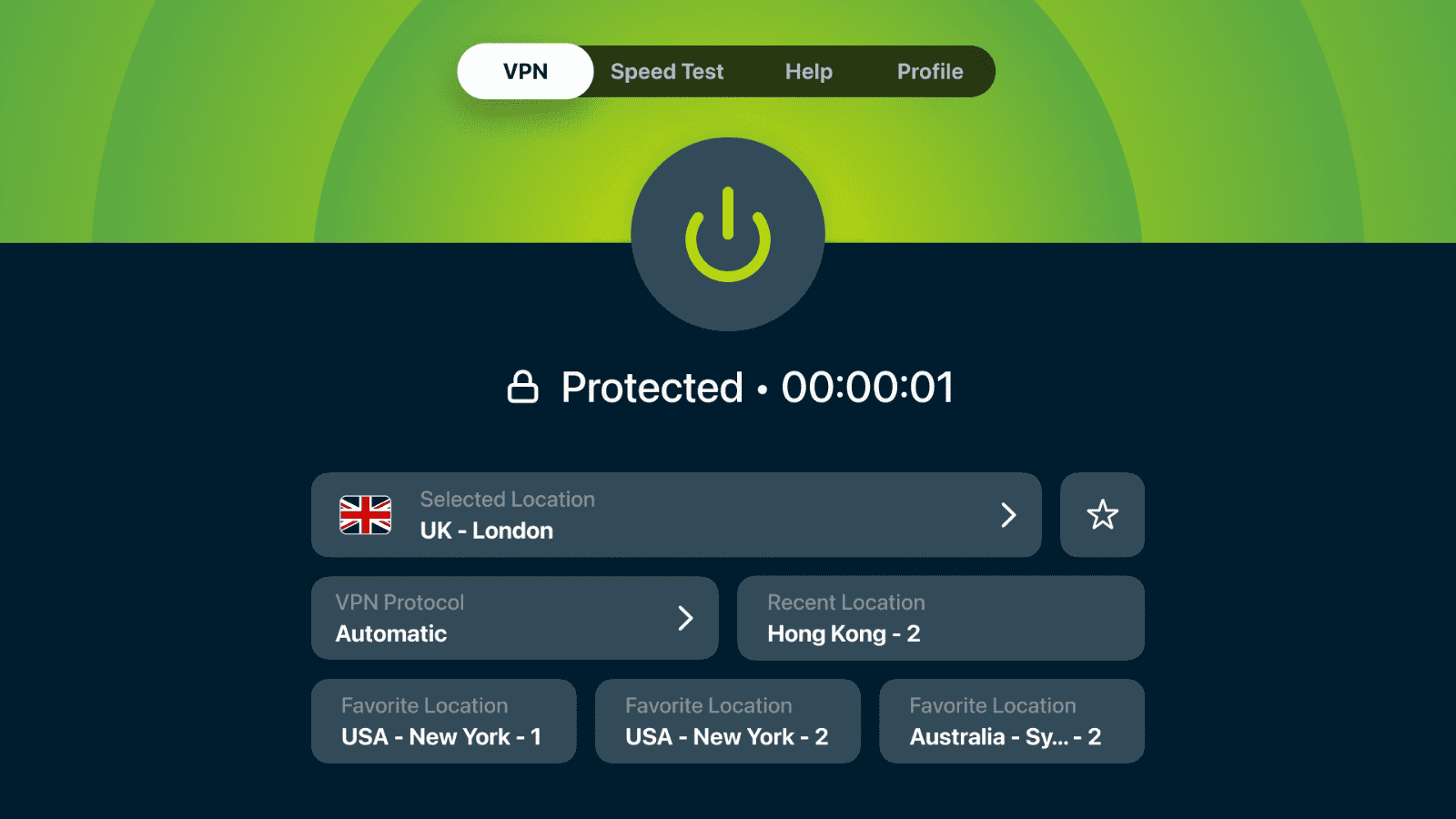
Key TakeawaysExpressVPN Apple TV app update: Introduces redesigned home screen, favorite locations, new protocols, and speed testing.Enhanced accessibility: Frequently used controls and saved locations now…

Key TakeawaysHentai Game Malware: Kaspersky discovered the Argamal malware family in April 2026, targeting players of hentai games with a full-featured RAT.Hundreds Infected: Victims were…

Key TakeawaysPhaaS Expansion: Arctic Wolf Labs observed Kali365 significantly expanding its Phishing-as-a-Service infrastructure across multiple platforms and brands.MAX Messenger Targeted: A fake prize-claim flow was…
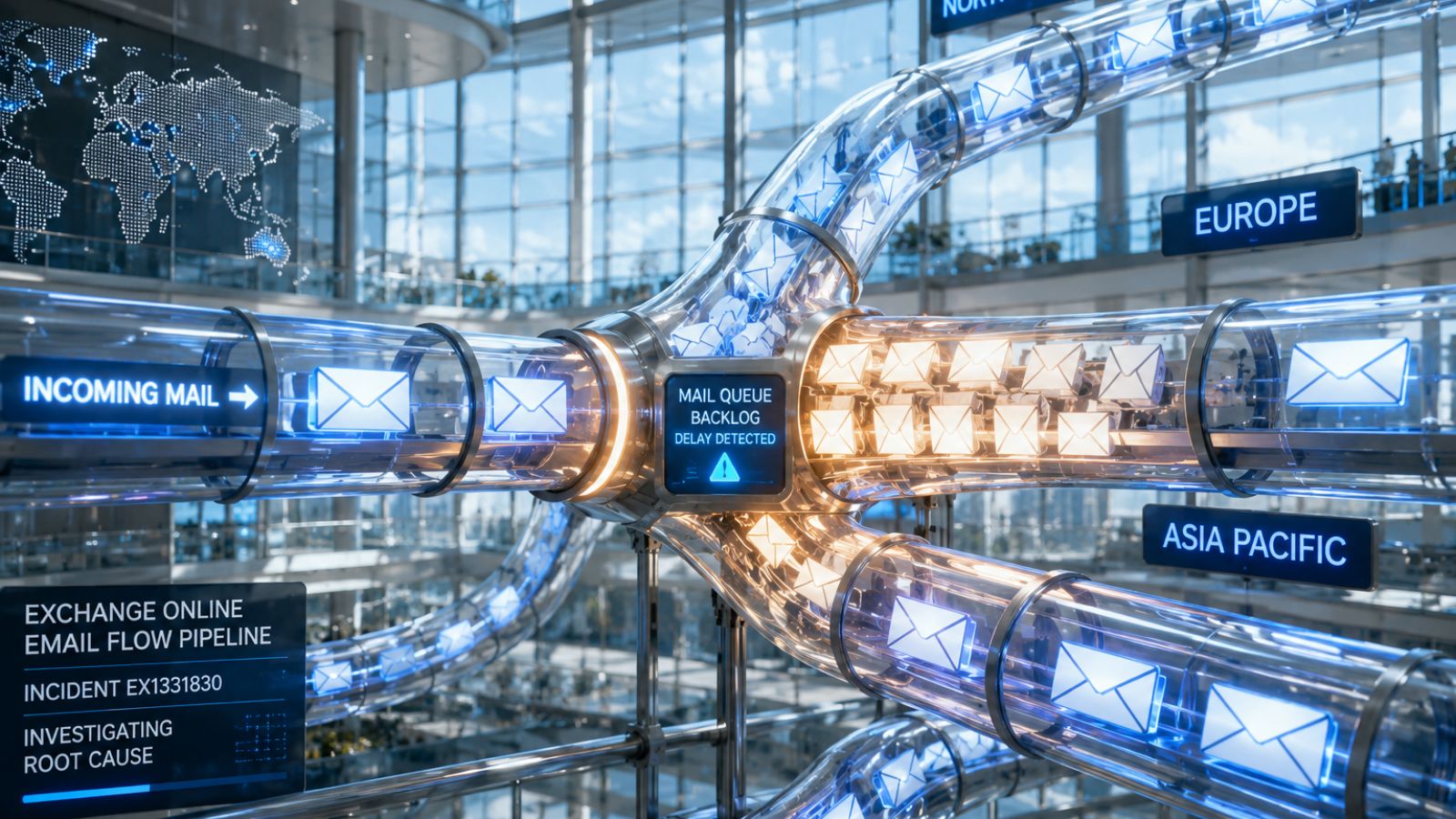
Key TakeawaysGlobal Mail Disruption: Microsoft Exchange Online experienced widespread email delivery failures across North America, Asia-Pacific, and Europe.Incident Tracking: Microsoft acknowledged the outage, tracked as…

Key TakeawaysCIS Rule Violated: Nova, the affiliate program for RAlord, accidentally infected Eriell Group, breaking the unwritten rule against targeting CIS organizations.Affiliate Consequences: The responsible…

Key TakeawaysLarge-Scale Infection: WeedHack has compromised more than 116,000 Minecraft systems since January 2026.MaaS Operation: The Minecraft-focused campaign operates as a Malware-as-a-Service infostealer with a…
Key TakeawaysCalifornia Social Media Ban Advances: California social media ban bill passed Assembly, moving to Senate review.Age Verification Requirements: Platforms must verify ages and prevent…

Key TakeawaysX-VPN No-Logs Audit: Independent review verified no traffic logs, activity tracking, or connection data retention.Privacy Controls: RAM-only servers, disabled logging systems, and automated controls…

Key TakeawaysTargeted Doxing Operation: The Spanish National Police arrested an individual for leaking sensitive data from critical government organizations.National Security Risk: The compromised information exposed…

Key TakeawaysAuthentication Controls Bypassed: Threat actors utilized brute-force attacks to circumvent 2FA mechanisms on specific user accounts.Encrypted Vaults Exfiltrated: Malicious actors successfully downloaded the encrypted…

Key TakeawaysSupply-Chain Compromise: Over 30 Red Hat npm packages were backdoored with a new variant of the Shai-Hulud dubbed Miasma.Credential Harvesting: The malicious payload targeted…