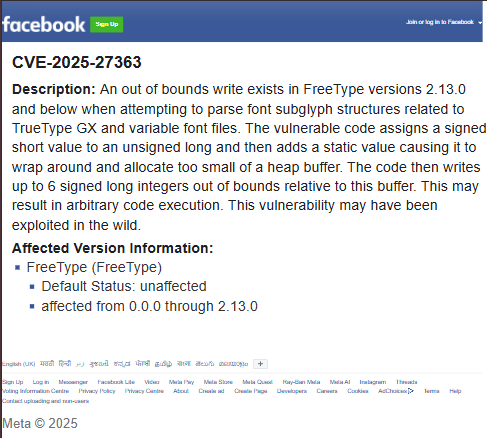
Facebook Says ‘FreeType’ Arbitrary Code Execution Vulnerability May Have Been Exploited in the Wild
- A flaw may threaten Facebook with unauthorized, third-party remote code execution.
- The critical out-of-bounds write vulnerability affects the FreeType font rendering library.
- Since it only affects versions 2.13.0 and below, users are advised to patch and update accordingly.
Meta recently warned of active exploitation risk regarding the critical flaw tracked as CVE-2025-27363 that affects Facebook’s FreeType open-source font rendering library. This out-of-bounds write issue could allow attackers to execute code remotely by exploiting certain font files.
The advisory details how the vulnerability, assigned a CVSS score of 8.1, occurs in FreeType versions 2.13.0 and below. While Meta has declined to provide specifics on the nature or scale of the exploitation, they acknowledged that the vulnerability "may have been exploited in the wild."
The flaw arises when parsing font ‘subglyph’ structures related to TrueType GX and variable font files.
Specifically, the vulnerability results when a signed short value is assigned to an unsigned long and a static value is added, causing a buffer overflow. The system writes up to six signed long out of bounds integers, potentially leading to arbitrary code execution.
Despite the mitigations in recent updates, this issue remains widespread due to several major Linux distributions still utilizing outdated versions of FreeType. The vulnerability has already been patched in FreeType versions beyond 2.13.0 almost two years ago, with the current stable release being 2.13.3
Given FreeType's critical role in rendering fonts across platforms, administrators and users are strongly urged to update to the latest FreeType version to mitigate the risk of exploitation.
For Linux distributions that do not yet offer updates, additional vigilance and proactive measures are recommended until patches are made available.
Meta is currently in the middle of a lawsuit that accuses Facebook’s parent company of training its artificial intelligence (AI) models via torrented content, with over 81TB of data downloaded via Anna’s Archive.