CISA and the FBI Publish Second Alert on the Conti Ransomware Group
- American cybersecurity agencies warn about Conti attacks being on the rise again.
- The most commonly exploited flaws by the group are “Zerologon” and “PrintNightmare”.
- Patching software and following standard security practices should be enough to thwart the threat.
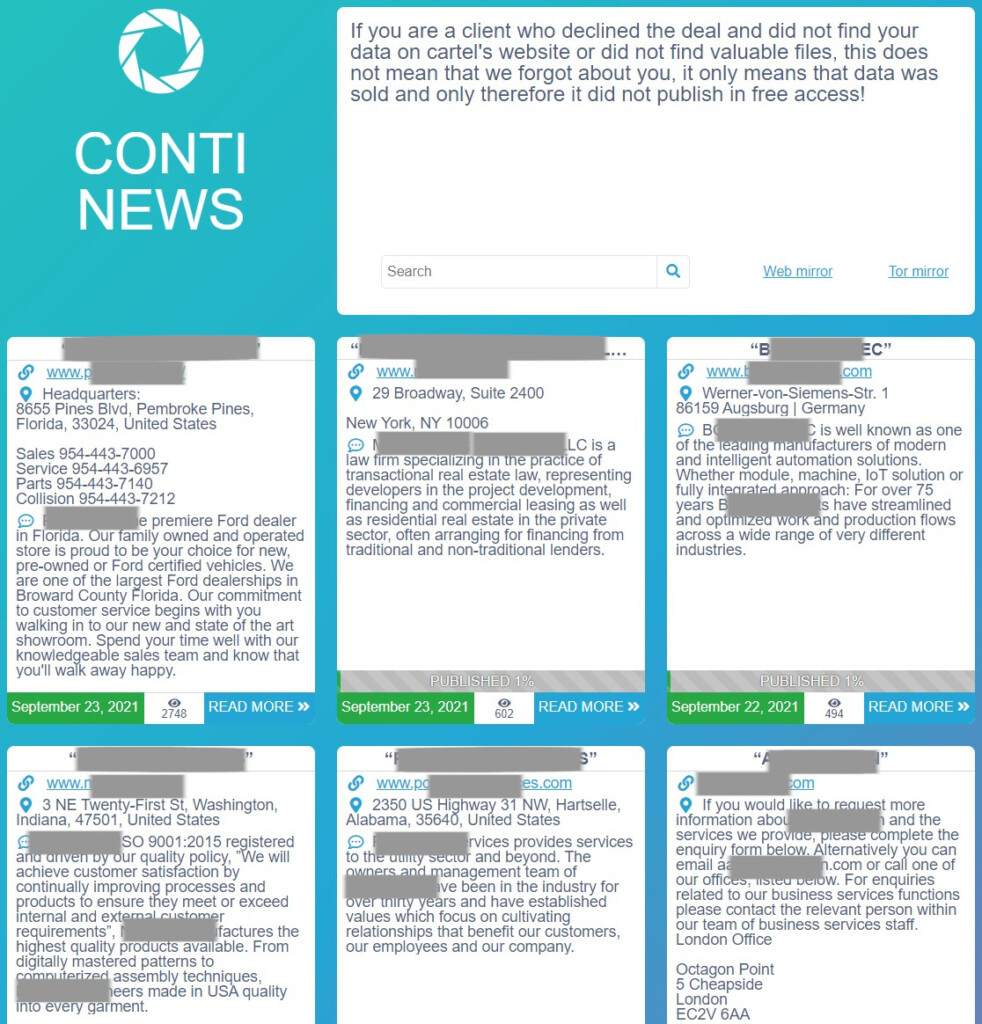
The Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI) were forced to publish their second alert about the Conti ransomware group in less than six months, as the activities of the particular group of actors are on the rise again. As the alert details, the agencies have observed the deployment of Conti’s file encryption malware in more than 400 attacks on U.S. and international organizations, with a significant percentage of those resulting in a success for the hackers.
The alert explains that Conti has various ways to break into target networks, as the RaaS is used by many affiliates who follow different tactics. Here are the most common ones that have been spotted in the wild:
- Spearphishing campaigns using tailored emails that contain malicious attachments or malicious links – Malicious Word attachments often contain embedded scripts that can be used to download or drop other malware—such as TrickBot and IcedID, and/or Cobalt Strike—to assist with lateral movement and later stages of the attack life cycle with the eventual goal of deploying Conti ransomware.
- Stolen or weak Remote Desktop Protocol (RDP) credentials
- Phone calls
- Fake software promoted via search engine optimization
- Other malware distribution networks (e.g., ZLoader)
- Common vulnerabilities in external assets.
The vulnerabilities that Conti actors have been exploiting lately are mainly the “Zerologon” flaw (CVE-2020-1472) in Microsoft Active Directory Domain Controller systems, the “PrintNightmare” flaw (CVE-2021-34527) in the Windows Print spooler service, and 2017 Microsoft Windows Server Message Block 1.0 server vulnerabilities. Patching these would shut the door to the actors, but CISA provides additional advice on top of that.
That would include using multi-factor authentication wherever possible, implementing network segmentation and filtering network traffic, scanning for flaws and applying updates as soon as possible, and removing unused user accounts and unnecessary applications. Finally, endpoint detection and response tools are considered a necessity today.